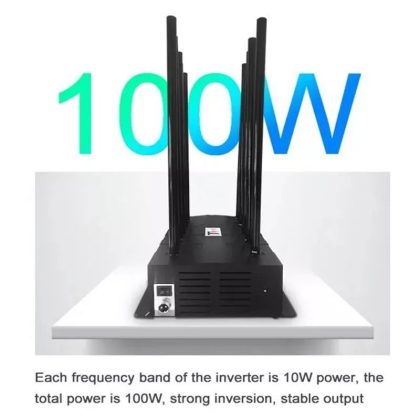
High Performance Rf Jammer With Gps Jammer, WiFi Jammer And Cell Phone Jammer Enhancements
Long Range Jammer Perfomance for 3G, 4G, 5G, WiFi, GPS, VHF, UHF, RC and Lojack. With 16 Bands, 16 Channels of Frequency Jammer Power.

RF Jammer
All frequency jammers are devices that emit an electromagnetic field designed to disrupt the operation of nearby frequencies. As a result, they can disrupt wireless communication in a defined area. They offer the distinct possibility of blocking eavesdropping and jamming wireless attackers. There’s been a heavy shift to using new wireless technology standards such as Bluetooth, low energy zigbee thread from Google, 802.15, RFID, and laura to name the popular ones. Here are some of the technologies; Bluetooth Low Energy, Zigbee, Thread, 802.15, RFID, LORS, just to name a few. Where the last thirty years has been about the internet, but the last 15 years has been focused on cell communications and WiFi. There’s now a big move to newer capabilities in IOT devices (Internet Of Things devices). The unknown fact is that many of the IOT devices you buy include a two-way radio frequency capability in them.
A nice multi-use frequency jammer to have in the home!
Works easy with nice features.
Exceptional value for the money. I Would recommend this radio frequency jammer.
Frequency Jammer
They don’t tell you that these 2-way radio transceivers are being linked together to form mesh networks that allow for data to be Mesh Networked forwarded over long distances without cost monitoring or an internet. In addition new sensors are being built into these common devices that are threatening our privacy in new ways while many of you are excited to check online for the next new IOT gadget.
Some bad guys could be looking to take advantage of this, and the bad guy can be the hacker or big tech collecting your private data, or new players wanting to capture your information. Independent of big tech in all of this, the unaware consumer is always the victim so in this read, I’ll give you a bigger picture of radio frequency technologies, that are in these devices, and what these radios can do. I will also answer the question about jamming these radio devices and their frequencies, later own, so keep on reading.
Signal Jammer Blocker
One of the reasons that I got into radio frequencies, is because I understood that the next level of cyber threats will come from and via the use of radio frequencies. Unlike in the past when communications over the air were analog voice signals or analog signalling using cw or morse code, things have changed significantly. Many of you take for granted that your WiFi signals cross the airwaves in digital form. Even your cell data communications are no longer sent with voice data. These are all digitized so that your voice comes out clear and is free from interference. Things like your car fob and garage door opener have been sending digitized signals as wel..
Signal Jammer Wifi
We are all used to wireless devices in the form of Bluetooth, which we’ve been using to connect headphones and speakers to our computers, phones and car audio. Wi-fi based devices independently pass video data on your network so you can monitor your house. Many of you have begun to use home automation products, which allow you to remote control your home electrical components. And devices technology appears to be moving forward. And you’re all enjoying the new capabilities of this modern world technology, but not everything is as it seems. These technologies extract a cost from society but before I get into specifics of the problem let me explain briefly how radio transmissions now get digital data in ham radio.
Premium Wifi Jammers & GPS Jammers
We feature quality frequency jammers with gps signal jamming capabiltiy all built-in.
Signal Jammer GPS
Much of the communications in the past, were done using voice over a microphone and this gets transmitted using modes like am amplitude modulation fm AM – Amplitude Modulation FM – Frequency Modulation SSB – Single Side Band frequency modulation and ssb single sideband these modes work differently depending on the frequency they have different strengths and weaknesses in the super low frequencies.
Radio Frequency Jammer
The most common long-range transmission is over am radio and using the am mode often at night an am broadcast in boston can be heard all over the eastern seaboard or all the way to chicago above am radio in the slightly higher frequencies used by ham radio HF Frequencies 1.8mhz – 25mhz called hf the transmission modes are usually based on ssb because there’s a lot of interference or noise in the reception and that is because hf radio relies on reflection from the ionosphere to allow long distance communications.
All Frequency Jammer
Reflections will often add in noise, so in hf radio we use ssb mode, ssb uses a very narrow bandwidth to eliminate the noise thus the name single sideband in the higher frequencies like vhf, uhf or microwave there’s less noise but the range is limited and the fm mode is used for transmission which is a wideband broadcast fm or frequency modulation as you hear on the car radio, has a clear sound and that’s because, this shifts in frequency inside a broadcast band is used to replicate the sound pattern rather than sending the voice data with a changing signal strength, as in am radio. And this allows it to exclude the noise the carrier signal. In fm it is fixed, in WiFi and digital communications these shifts and frequency are now used to send zeros and ones often with clarity. One of the common modes used for converting radio data to digital is called fsk or FSK – Frequency Shift Keying. Frequency shift keying which is used over fm, in other words a fixed carrier signal shifting between two frequencies can signify a zero and a one inside the broadcast of fm fsk, is still heavily used now in ham radio. Many transceiver chips are cheaply made with an fsk FSK Encoder/Decoder encoder decoder or another mode is psk encoder decoder known as phase shift keying. Psk is used in WiFi within certain frequencies these modes are very reliable for communications today.
Longer Range Cellphone Jammers
Signal Jammer Mobile With GPS Jammer – 12 Channel’s

Quality Rf Jammers
2 Year Warranty On All Frequency Jammers
Military Radio Jammer
Device to device communications are clustered in certain frequencies 433 megahertz 433mhz, 900mhz, 2.4ghz, 5ghz 900 megahertz in some countries 2.4 gigahertz and 5 gigahertz both worldwide. The reason for the clustering is that these devices are using what is known as an ISM band, (industrial scientific and medical band). These are bands reserved by the fcc and other worldwide regulators for these devices what is characteristic of this ban is that the use of these frequencies is by unlicensed users however, the devices have to get FCC certification in the United States. In the lower frequencies below 1 gigahertz. Typically the protocol used is LoRa – Long Range (Proprietary) long range the other transmission protocols like Bluetooth reside in the 2.4 gigahertz and above.
Frequency Jammer Device
Radio jamming devices are commonly used to disrupt the radio signals and deny access to a specific area or frequencies. They can be used in both military and civilian purposes, but are most common in law enforcement and security personnel. There are a few different types of radio wave jammers available, but the most common are those that emit electromagnetic interference (EMI) frequencies and signals that will disrupt or block the transmission of radio frequency signals.
A Few Featured Devices For Jamming Radio Signals
VHF Jammer
Most of you are quite familiar with 2.4 gigahertz and 5 or 5.8 gigahertz when used with WiFi, which is another form of an ISM device that is intended to be connected to the internet. Another thing to note is that radio transceivers and communications technology is sold as a system on a Chip or SOC, in other words there will not be separate components inside the IOT device motherboard. It will be integrated with the CPU. So, it does not cost extra to have these radio transceivers included in the device.
433 Mhz Jammer
Normally your own devices transmit only your traffic meaning the security cameras intended to send your video footage to you only. But the new trend is to piggyback data over your existing devices to other people’s data, basically using your device to provide a radio network for data to flow from device to device.
Signal Jammer
The way this works is that devices are built with the capability of receiving commands on the air as well as forwarding messages intended for other devices. I refer to this as OOB or (out-of-band), Out of Band Data traffic, since it is not your traffic, but somebody else’s. Each device can receive a message which it can read using the FSK decoder for example, then it retransmits the message over the air, if the message is not intended for itself again using the FSK encoder for transmission. In this way a message on a particular frequency can be propagated over a large distance by seemingly innocuous devices like an IOT light bulb, a motion sensor or an outdoor light switch. So what do you do, if you want to use a signal jammer and start jamming rf signals? Keep reading, there are many reasonable options that you can employ to utilize a signal jammer in the best of ways.
Frequency Scrambler
There are ways to ensure that radio traffic is limited first the transmissions have to be very short since the speed of transmission using fsk is very slow then there’s a ttl, or time to lift parameter included, that gives the message a lifespan, so it doesn’t propagate forever. Additionally each message uniquely identifies the original device sender so basically a low bandwidth method is now available to send messages anywhere within range of these radio devices typically maxed to one half mile, but can hop to unlimited distances if there are other devices in the area that can retransmit.
Jamming Radio Signals
Many devices have built in Bluetooth, this includes of course phones, cars, TV’s and various audio appliances like, Amazon Echo. These devices use a communication standard called Bluetooth “Classic” (short range) to transmit large amounts of data within a short range. The range of a personal space which is within about 10 feet. Well surprisingly a new standard was developed that can transmit a stronger signal for short bursts, and this new standard has a range of one-half mile but the interesting detail is that it is using the same Bluetooth radio. This particular standard is called Bluetooth low energy or BLE and with this BLE – Bluetooth Low Energy capability, any device with Bluetooth can now transmit data to a one-half mile range with just a software change.



2.4 Ghz Frequency Jammer
I already wrote in a earlier blog post, explaining how this was done to Amazon echos and ring cameras. What I didn’t tell you was that Bluetooth, was also built into TVs and now with a software change your Smart TV cannot communicate with other BLE devices, without your knowledge. ATV can also be forwarding messages from device to device all day long, over a very large area until the data reaches some data collection device. As it turns out this capability is actually being planned right now. Broadcast TV will not only send you a digital broadcast it will also be able to get feedback from your tv just like in the book 1984, where you talk back to your tv while being monitored by big brother.
But, big brother will now be the Nielsen Ratings. And I checked the TV manufacturers Samsung, Vizio, LG and others, and they are listed as adopters and sponsors of Bluetooth. This communication from device to device has become very sophisticated.Forming a separate network which is called a mesh network is a peer-to-peer network with no home base the ble powers the mesh network known as the Bluetooth Mesh Network.
Jamming Rf Signals
Bluetooth Mesh Network is how it gets the range, but in case you think this is the only mesh, there are actually many more, one of them is thread mesh. Thread Mesh by Google has shared a source code of thread and calls it open thread. This particular protocol is even more sophisticated than Bluetooth mesh network because, it includes specific device addressing using ipv6, a standard networking protocol we are familiar with, on the internet. This is a technology built into Google nest, so each device is addressable and identifiable to the group by an ipv6 address, which also allows a clear pathway from point to point. The message forwarding has been enhanced, like its on steroids.
What Our Customers Say
High Frequency Blocker
What is interesting about the use of these technologies, which include BLE, Thread, Zigbee and 802.15. They can be used on devices that are battery operated and, the battery can power it for a year or more. And of course, unlimited times if the devices comes with a small solar panel. The devices are then independent and self-powered for longer periods, portable and cheap.
These devices also have a direction finding element, so Direction Finding/Geolocation frequency signals, will be detected directionally. It will be possible to specifically target devices within a particular direction. Direction finding for example, is built into Apple Air Tag and likely the tile trackers, so you not only know a device is near but specifically where it is. Geolocation is built into the capability of even the lower frequency ranges used by Laura, just to make it clear, these devices can not only forward messages within a sophisticated mesh network, with addressing capabilities, but the location of each device will also be known since, that is part of the protocol capabilities.
Wifi Signal Jamming
So without your knowledge you are buying Smart Devices with built-in radio transceivers, that can both send and receive other people’s traffic, and this includes your toaster, your camera, your motion sensor, your TV, your refrigerator, your doorbell. So it should now be obvious that devices become capable of transmitting usage over the air via frequencies. If you change your TV to a different channel, you might expect it to transmit that over the mesh network. If your motion detector detects a motion, or your outdoor camera turns on, then it can be capable of sending this signal to other devices, other devices that will forward that data as out-of-band traffic, to some unknown destination. Also programmed into the device in another post, I talked about RFID and how an RFID can be detected by normal equipment within 200 feet. If it is the standard commercial gen 2 RFID, but with merely a software change devices can include the code to also send an RFID signal and then, read a response back. Since these are also in the same frequencies as the radius building to many of these existing devices.
Wifi Signal Jammer
This leads me to introduce you, to the topic of sensors. RFID’s could be read over long distances and track you by sending the data over the mesh network. In case you didn’t know if you have an enhanced driver’s license in the United State or carrying a recent USA passport then there is an RFID on your person, even the tires on your car have an RFID. This means that it is possible that, by embedding software in common devices perhaps even installing software updates, without changing devices, some entities could re purpose your devices, for spying. One of the easy targets for this is your Smart TV.
Smart TV’s get software updates regularly and some TV’s can even watch you, since some brands have cameras, that are used to switch the devices on and off, based on who’s in the room. And again, the average consumer is not aware of these things, that you are reading. It would be possible to activate a surveillance system capable of tracking any person’s movements anywhere, with precision, in case you think you can only be tracked by RFID, then let me tell you about several other radio frequency emissions that occur on or about your person.



Wifi Blocker For Home
Your phone sends a regular beacon over several different frequencies. The most common one, is over WiFi. The beacon announces your mac address, which is a unique identifier to your device, and it is possible to determine how many times you visit a local Walmart, just by listening to the WiFi mac address and recording it. The Mac address is unique and it will point to you specifically. Another mac address is also broadcasting over your Bluetooth. There’s an open source project called Wiggle, which stands for wireless network mapping and they record every mac address detected by people sensing mac addresses, in the area. Check out www.wiggle(dot)net, so you can see for yourself, this is not theoretical that mac addresses, can be recorded, and the Wiggle project demonstrates it.
In fact a Walmart could use the same software, and what changes now, is that mac addresses can now be collected and forwarded to a repository automatically, over the mesh networks, that have been created, over long distances. And with Geo location cameras, record videos, but specifically ring cameras will share the videos, in a central database to law enforcement and or their contractors. And don’t dismiss the importance of those contractors, because some of the largest contractors are Palantir, Google and Amazon, which will have direct access to the videos. But the point is that the videos collected from certain cameras like Ring and perhaps the Google Nest cameras as well, are centralized, combining this with Geo-location data, the mac address data, and RFID data, it becomes possible for other agencies, Big Tech and these contractors, to track your movements by matching video, with the presence of secondary identifiers. I think this was in the movie Eagle Eye (1984).
Pocket Wifi Jammer
That happened in 2008, now it is actually real, if you think these sensors that detect this kind of data is good enough, think again there’s always more. Researchers have already found that someone, can do the equivalent of performing a X-Ray on your home, using WiFi frequencies, and it can be used to detect movements like infrared, and of course many homes already have infrared sensors, so that would be added in, but since WiFi frequencies are in the same capability, of the existing radio transceivers, then again they could be used to sense occupancy as well, which is one reason for a WiFi signal jammer or wifi disruptor. And once again this personal data can also be forwarded over the mesh network, to some central repository. In the case of Amazon the central repository is called Amazon Sidewalk. Google of course is the repository of the thread mesh Google’s Thread, which is what is used in Google nest but there’s nothing particularly unique about that technology.
Jamming Radio Signals
Any third party could come up with its own private mesh network and forward messages using its own devices implanted in your house. For example Smart TV’s could be built with an entirely independent mesh network, that’s not beholden to Google or Amazon or Bluetooth, so basically any popular device could be built with a mesh, and if it is popular enough, it could provide the coverage for large areas. We assume here, that the security protocols built into Bluetooth mesh thread by Google and Amazon Sidewalk, or the Apple Air Tag Network are secure, but as we know hackers will often find a hole and we only know about it, when it is discovered. No one discovered that a certain agency turned your Samsung TV’s into a listening device that can hear your conversations through the TV speaker, In other words they turned a speaker into a microphone simply with software.
There was no hardware wiring required if the TV has a camera that could be hacked. And we already know that many security cameras have been hacked and the video from many baby monitors as well, were re-broadcast over the internet. But the difference today, is that the average consumer has made their homes dense with electronic sensors and IOT devices without the understanding that, each device can communicate independently over various frequencies, with their own independent radios, outside of the user’s home.
Think about this; How much effort and cost would it take to install IOT sensors at each light pole in a city. One that can track devices electronically and forward messages via different frequencies, without wiring or internet by using existing technology. This is very inexpensive to do and by simply attaching a device to each light post, without wiring and a small solar panel, it can provide unlimited years of power for the device.
Signal Jammer Mobile With GPS Jammer
Okay now let’s switch gears to the question that’s often raised, which is can you jam these frequencies? Quite a few people constantly ask if you can Jam these frequencies, and the answer is yes, you can jam the frequencies in question, and there are many hardware tools you can buy, that can do this. But just to be clear that jamming is restricted and there are roving fcc vehicles with the ability to triangulate any strong continuous jamming transmission, if there is a bad guy, causing very strong rf disruption over a large area, the culprit can be found. But, if you are a licensed ham operator you can legally transmit all the frequencies used by ISM devices, in a home laboratory environment, where the signal is attenuated to affect only a personal space, then it would affect only that person and their localized area, and would not be detectable outside of their home area.
Radio Frequency Blocker
But the bottom line when it comes down to a jammer; there are a quite a few different reasons why someone may need or want to use a directional wifi jammer or frequency disruptor. For example, they may need to block certain transmissions from a hostile local location so that friendly frequencies can operate without interference. Or, they may need to prevent a rival company from stealing their trade secrets by disrupting and maybe penetrating the communication networks. Some Law enforcement and private security personnel also use them as a form of large crowd control situations. By disrupting and or shutting down the communications in an area, they can usually discourage people from congregating and causing riots.
Frequency Blocker
In other situations, a rf jammer is used to disrupt communications between hostile forces and their controllers. And obviously this can be very useful in military operations or during a hostage situation, where a hostage needs to be able to communicate freely without being overheard. The radio frequency scrambler can also be used to block illegal transmissions, like unauthorized broadcasts or conversations. Another benefit of a multi frequency jammer is that it can be used for personal protection. This is especially useful in areas where mobile phone devices as well as Wi-Fi signals are strong. But, by disrupting or blocking these signals, you can protect yourself from cyberattacks and other forms of electronic surveillance.
Frequency Disruptor
Vhf jammer devices can help protect critical infrastructure and prevent many malicious attacks. They are used by some government institutions, businesses, and individuals to prevent the unauthorized intrusion into or interference with systems or networks. High frequency jammers are also used to disrupt or disable wireless communication. The devices are becoming more and more common, with some law enforcement agencies using them to interfere with the cell phone service and or some Wi-Fi networks. There are also many other organizations and some groups that use broad spectrum frequency jammers for nefarious purposes, such as disrupting certain frequency communications.
FM Radio Jammer
There are a many reasons why people may want to use an low frequency jammer. Some may use them to prevent other from tracking their movements or intercepting their communications and they can also be used for other purposes, such as disrupting eavesdropping equipment. There are a number of ways to utilize RF jammers. The first is to be aware of their purpose and what they can do and take appropriate precautions. Anyone who uses wireless devices should also take precautions, such as not using proximity when possible and restricting access to their device if it is not in use.
Radio Jammer For Sale
If you’re like most people, you’ve probably never given much thought to jammer frequency ranges. But if you work in high-security settings or live in an apartment building where rf blocking is sometimes needed, then the time to start thinking about these devices is now. 2.4 ghz frequency jammer are becoming increasingly popular for unscrupulous people to break into stores and apartments, but they can also be used as other types of tools of anti-crime to protect confidential information. So if you want to keep your personal information safe or if you have a need to prevent gps tracking when outdoors and about, it’s important that you learn a little more about radio frequency disruptors and how best to use them, especially a gps signal jammer for car. Instead of buying the first radio jamming device for sale, that you see, check the frequency ranges that they will best work for and then make a better informed decision from there.
It is now possible to surveil and track, every move a person makes and some say, we have no right to our privacy. If you believe what they say, then keep on buying these kinds of devices, and don’t bother to make a distinction about their hidden capabilities. It’s obvious that this new technology can be used for good, but the problem is that, when power of control is given to a few, then chances are this power will be abused. Continue to do research on radio frequencies, how to best utilize a rf jammer and how to mitigate its negative affects on you and your life. You owe it to yourself to be as well informed as possible, about these newer IOT and Smart technologies, and the potential of abuse, in this new threat arena. I hope you found this post to be of value.